Security & privacy
What Teleperson collects, what we don't, and how the data we hold is protected.
This page is the public, plain-English summary of how Teleperson handles your data. It is intentionally short. The full technical architecture lives in our internal threat-model and data-handling documents, audited as we ship.
What Teleperson sees
| Data | When | Where it goes |
|---|---|---|
| Public page metadata (URL, title, OG tags) | When the panel opens on a site | Used to identify the company; metadata for new companies is sent to our backend to enrich the shared catalog. |
| Your Hub (followed companies) | When you follow a company | Stored in Postgres, scoped to your user via row-level security. |
| Your profile (first name, age range, signup reasons, plan) | When you sign up or update your profile | Stored in Postgres, RLS-scoped. Demographic fields are optional. |
| Plaid access tokens (when you link a bank/card) | When you complete Plaid Link | Never seen by the extension. Exchanged server-side, encrypted with AES-256-GCM at rest. |
| Stripe subscription state | When you upgrade | Stored in Postgres; raw card data is never seen by Teleperson. |
| Voice Concierge transcripts | During an active voice call | Streamed live in the panel for your reference. Persistence is opt-in. |
| Chat co-pilot conversations | When you actively run the co-pilot | Stays in chrome.storage (device-local) by default. Backend recording is opt-in. |
What Teleperson never sees
- Page content when the side panel is closed. No background scraping.
- Authenticated session cookies or tokens for the sites you visit.
- Form input — what you type into a company's site. The content script reads metadata, not form fields.
- Bank credentials. Plaid handles the credential exchange. Teleperson receives access tokens after Plaid has authenticated you, never the username/password itself.
- Raw card numbers. Stripe handles all PCI-scope data. We see Stripe's customer/subscription IDs, not card data.
How tokens are protected
- Plaid access tokens are encrypted with AES-256-GCM before being written to Postgres, with a per-token random IV. Plaintext access tokens exist only for the duration of an Edge Function request.
- Vendor account access tokens (eBay, Shopify partner stores, etc.) follow the same AES-256-GCM pattern with a separate encryption key.
- Extension auth tokens (the
tle_…strings used in theX-TLE-Tokenheader) are stored as SHA-256 hashes in Postgres. We can verify a token but never recover it; lost tokens require a new issuance from/ConnectExtension. - Row-level security is enforced on every table holding user data. A compromised credential can only ever access its own user's rows.
How we handle AI calls
- Cached overviews. Company-level AI overviews are generated once per company and cached. Your visit to a company that has already been overviewed does not produce an Anthropic call.
- Ask AI prompts route through the Teleperson backend by default. The backend logs only metadata (latency, token counts, outcome) — never your prompt text or Claude's response.
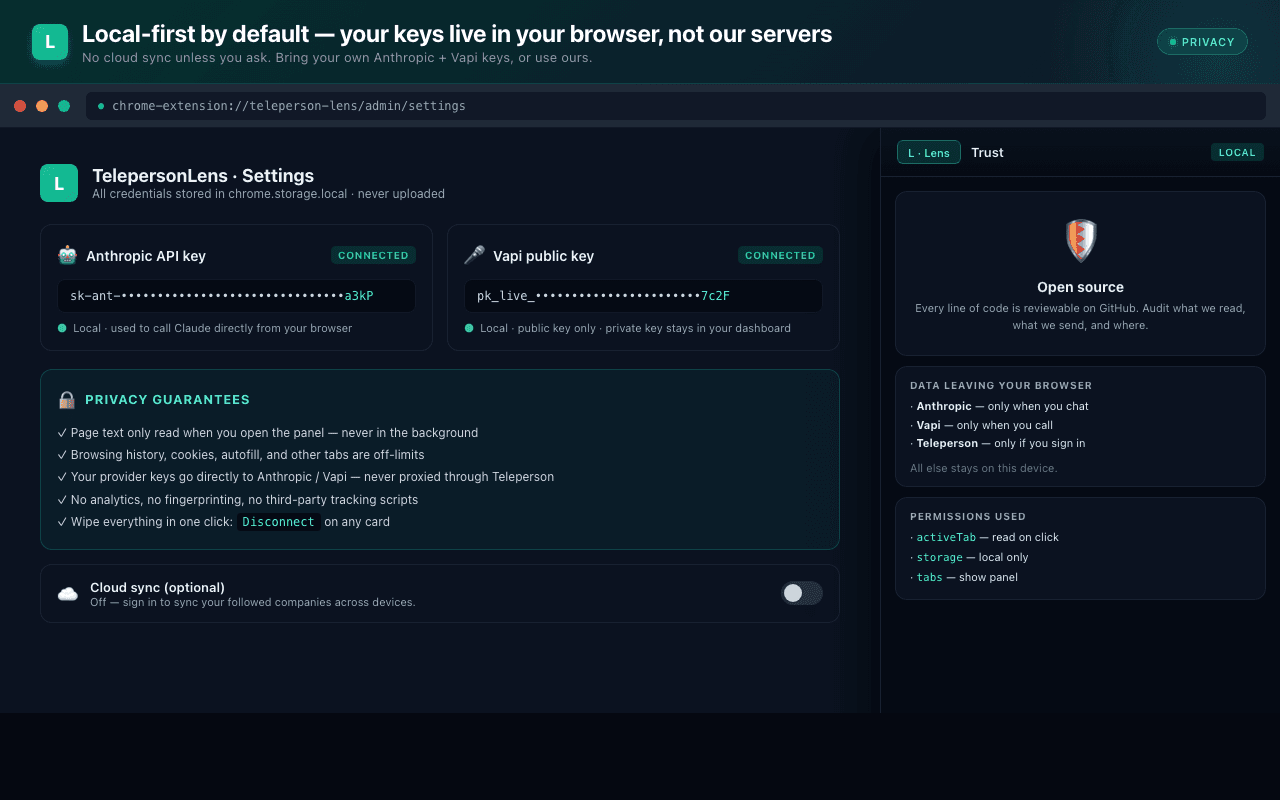
- BYO API key mode. Power users can configure their own Anthropic API key in admin settings, in which case Ask AI calls go directly from the extension to Anthropic. The Teleperson backend is bypassed entirely.
How chat co-pilot stays safe
When the chat co-pilot is active on a company's chatbot widget, every drafted
reply is run through a binding-action classifier before the Send button
is enabled. Classified categories: cancellation, payment_change,
contract_change, escalation, safe. Drafts that would create commitments
require an explicit "I authorize this" toggle before Send is enabled. Parse
failures default-deny.
A persistent Stop button at the top of the panel detaches the chatbot observer in one click; nothing the agent has drafted can be sent without your click.
Disconnect = deletion
When you disconnect a Plaid item or a vendor account:
- We attempt to revoke the token at the third party (best-effort).
- We delete every row scoped to that connection: tokens, transactions, orders, shipments, invoices.
- We append an entry to our internal audit log so we can prove the deletion.
Disconnecting is not a soft delete. The data is gone.
Reporting a security issue
We take security reports seriously. Email security@teleperson.com with details. Please include reproduction steps and any proof-of-concept payloads. We respond within one business day and offer credit (with permission) in our release notes.
Related
- System overview → — the architecture this security model lives in.